Your password must be at least 8 characters long, contain a mixture of uppercase and lowercase letters, and include at least one number or symbol
2 May 2020
Familiar with password forms like this?
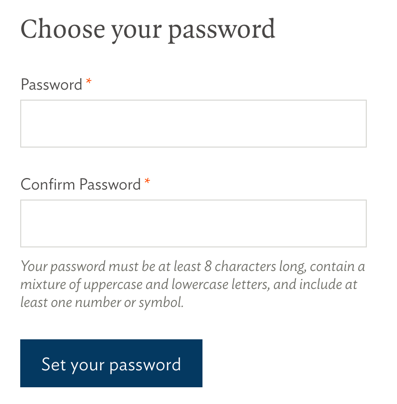
Restrictive password rules are not just frustating and unhelpful for people trying to manage logins for a multitude of sites; they (officially) do not do much for security on your website.